¶ Independent IT Audit — Scope, Method & Deliverables (UK)
¶ Introduction — What an Independent IT Audit Delivers
An independent IT audit gives your organisation a clear, vendor-neutral view of your current IT environment, highlighting where risks, gaps and inefficiencies truly exist.
It provides a prioritised, actionable plan you can implement without adding complexity.
What it does not do:
- Attempt to sell tools or products
- Apply a one-size-fits-all checklist
- Overwhelm decision-makers with irrelevant technical detail
¶ What You’ll Get (Outcomes)
¶ Clear, Actionable Deliverables
- A concise report in plain English (or French)
- A prioritised action plan (risk • impact • effort • cost)
- Practical recommendations executable internally or with existing suppliers
- Optional: governance follow-up, delegated IT, or project support
¶ Audit Process — 4-Step Methodology
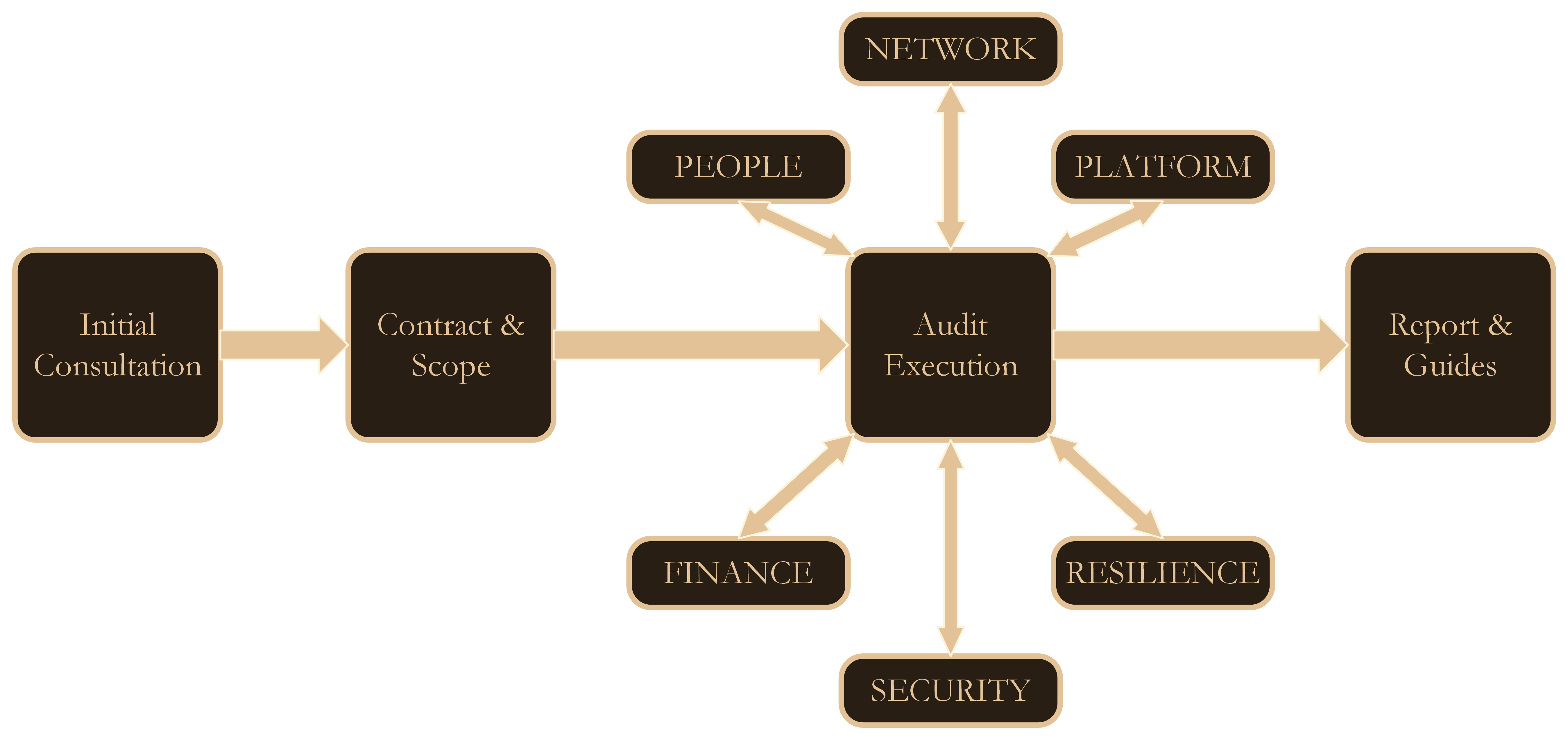
¶ 1. Initial Consultation
¶ Purpose
Understand goals, constraints, symptoms and the right audit scope. The discussion will be hosted by a senior IT Consultant.
¶ Format
- 30‑minute (minimum) video call (Teams/Zoom) → book here: https://www.brimbor-consulting.com/contact
- NDA available before any information exchange
- No sales pressure
¶ Outcome
Shared understanding and agreement on scope and next steps.
¶ 2. Contract & Scope
¶ What We Define Together
- Scope and boundaries
- Pricing (fixed scope or capped day‑rate)
- Timeline and stakeholder availability
- Access requirements (read‑only; no privileged access needed)
- Deliverables and report format
¶ Outputs
- Confirmed engagement
- Clear timeline
- Audit checklist tailored to your context
¶ 3. Audit Execution
Remote‑first to reduce disruption; on‑site only when it adds real value. Discussed during the scope definition.
¶ 3.1 People
- Internal roles, responsibilities and skills
- External providers: accountability and service fit
- Users: needs, pain points, friction in daily activities
¶ 3.2 Network
- LAN/WAN/VLAN/WLAN
- Inter‑site connectivity and routing
- Wi‑Fi reliability
- VPN/remote access
- Internet links and failover
- Optional IP‑based services: printing, VoIP, CCTV, streaming
(Read the free resources)
¶ 3.3 Platform
- Servers (on‑premises, hosted, virtualised)
- Logs, roles, policies and configuration hygiene
- Cloud posture: governance, identity, cost control
- Physical environment: power, cooling, physical access
¶ 3.4 Finance
- Cost‑per‑user and contract structure
- Subscriptions and amortisation
- Opportunities for savings without reducing reliability
¶ 3.5 Resilience
- Backup, continuity and recovery readiness
- Restore tests and separation from production
¶ 3.6 Security
- Identity & access
- Firewall and proxy posture
- External access paths
- Endpoint protection (AV/EDR)
- Policy and documentation maturity
¶ 4. Report & Recommendations
¶ What You Receive
- Executive summary (plain English/French)
- Prioritised plan (risk • business impact • effort • cost)
- Technical appendix with evidence, findings and diagrams
¶ Optional Follow-Up
- Delegated IT (lightweight governance, KPIs)
- Assistance with recruitment or team structure
- Coordination with existing suppliers
- Project support for migrations or remediation
¶ How Work Is Prioritised
We use a simple, transparent model:
- Risk — likelihood and impact
- Business impact — continuity, compliance, cost, user experience
- Effort — time and complexity for your team or providers
- Cost — licences, services, project resources
¶ What We Avoid (By Design)
- Vendor bias or reseller incentives
- Intrusive scans unless requested and scheduled
- Uselessly long reports
- Unnecessary complexity
¶ After the Audit — Typical Paths
¶ 1. Execute Internally
We remain available for clarification.
¶ 2. Coordinate with Your Providers
We help validate decisions and guide implementation when needed.
¶ 3. Delegate Governance
Regular check‑ins, KPIs and senior leadership support.
→ See: /delegated-it
¶ Frequently Asked Questions (Short Answers)
¶ Will this disrupt operations?
Minimal disruption: short sessions, remote‑first, on‑site only when it adds value.
¶ How is it priced?
Fixed scope when possible, or capped day‑rate.
¶ Can you work with existing suppliers?
Yes — full vendor neutrality.
¶ What access do you need?
Read‑only access and structured conversations with key staff.